A Brief Study on Printer Securities and Apex’s Chips Solution
A Brief Study on Printer Securities and Apex’s Chips Solution
(By the Marketing Staff at Apex Microelectronics)
The concept of the “paperless and digitized office” has been proposed for more than 30 years yet the printer is still the most important piece of office equipment.
With the popularity of the Internet, mobile accessibility and the development of IoT technology, printers have become more able to access a company’s network.
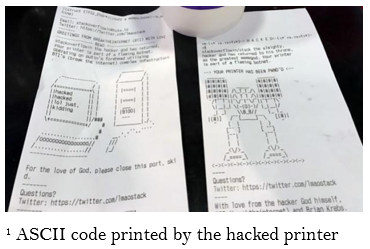
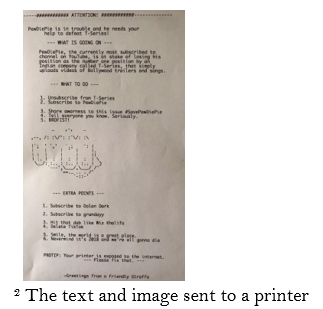
Printers have become a target for hackers because printed materials may contain a certain amount of important, confidential information. In February 2017, the hacker “Stackoverflowin” hacked more than 150,000 networked printers that were publicly exposed to the Internet and warned people to pay attention to printer security issues by printing ASCII code1. In December 2018, an anonymous hacker hijacked 50,000 printers around the world and instructed them to print subscription flyers for a YouTube channel named PewDiePie, an advertisement for his favorite YouTube channel2. Printers do face an information leaking risk, which can threaten the information security for individuals, businesses, hospitals, the military, banks, governments, and other organizations.
There are many ways to attack a printer, such as DoS attack, access to print jobs and even access to the company’s network. From the printer itself, there are five major gateways that can cause information leakage including print data transmission leak, print consumable leak, printer memory leak, printer software, and hardware leak, as well as print control and management leak.
Print data transmission leak refers to the data sent to the printer through the transmission medium after the user initiates the print job.
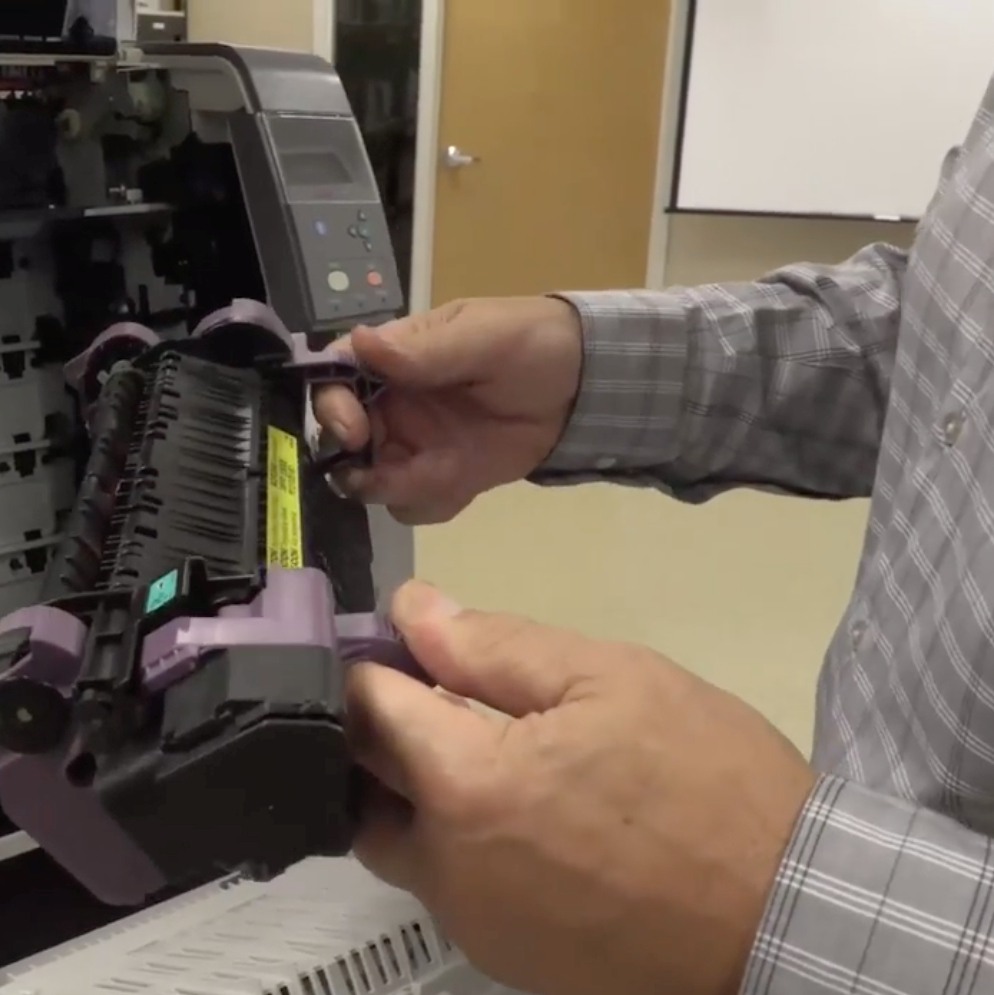
There are three risk points of communication interface, network access, and data transmission. And if a printer uses consumables with chips, there is a risk of illegally storing and transmitting information under the condition of storage and wireless communication module—this is what we call print consumable leak.
Printer memory leak means information can be leaked from the printer’s memorizer such as internal storage, memory card and files from the hard disk. All of this can cause memory data leakage and permanent memory leakage. It is easy to implant malicious code into the main control and management system because of its uncontrollable security. Firmware upgrades can also cause leakage as a result of malicious code. Print control and management leak refer to potential information leakage caused by untimely control and unpredictable permissions on the printing device.
In the face of increasingly complex situations internationally, it is especially important for printer manufacturers and consumable manufacturers to provide safe and reliable products to ensure the information security of users. The core component of a printer is the main control chip which is a special ASIC control chip.
In order to break the technical bottleneck of the printer’s main control chip, Apex has been cooperating with Pantum Electronics, Zhejiang University, and Hangzhou Zhongtian Microsystems to carry out a collaborative innovation of production, education and research since 2012. In 2017, Apex successfully developed a 4 cores main control SoC chip HSP2220 for use in multi-function laser printers based on UMC 40 nanometre technology. The HSP2220 is equipped with a high-performance CK810F CPU that supports processing system downloads and Linux operating system. It is equipped with a low-power consumption CK803S CPU that supports real-time response from printers and scanning interfaces. The chip has a complete system IP and peripheral IP, with a flexible image processing engine.
In addition, the chip comes with the self-developed security kernel CK802, which is a digital security concept based on secure SoC applications, with rich encryption modules (AES, DES, SHA, SM2/4, etc.). It supports anti-fuse OTP for key storage and CPU restricted access and has the ability to protect program execution and data operations from external attacks.
From the print consumables perspective, Apex’s own patented SoC chips use CPU core of 32-bit RSIC instruction set. The SoC chips are safe and not easy to be cracked or counterfeited by using the AES encryption algorithm. What’s more, Apex can also customize a dedicated chip for users to provide zero-confidence risk consumable chips for confidential units.
In our current world, the Internet can intelligently connect everything to everything. There may be information security risks in the transmission and connection process between data/information and smart devices. Especially in the era of the Internet of Things and Internet of Vehicles, every node can become a node for information leakage. Apex has 15 years’ experience in integrated circuit design and has comprehensive, mature and stable independent R&D design capabilities in SoC chips. With its strong resources and rich practical experience in chip security and encryption technology, Apex is launching important strategic deployment in the field of security chips.
In 2018, Apex released the first 32-bit secure high-speed network security chip with a dual-CPU core. One core is for security, and the other is for application. Application and security are physically isolated and cannot be cloned. The 256-bit SRAM-PUF chip supports two-way identity authentication with system integrity detection and self-recovery technology. It also supports multiple network security protocols (IPSec, SSL, MACSec, etc.) and international standard cryptographic algorithms (AES, DES, ECC, RSA, SHA, etc.), as well as a rich user interface to prevent information from being tampered, forged and leaked, which ensures the security and reliability of information. Apex has successfully bid for the China Southern Power Grid’s power distribution security chip project using its first dual-core network security chip which is now under the demonstration phase of operations.
In the future, Apex will continue to develop printer master SoC security chips for printing consumables and multi-core network security chips. It will invest more in these fields in order to intensify and go deeper on product structure and to improve product performance. Apex’s vision is to create a healthy, orderly and secure IoT information world, and to promote the rapid growth and development of the independent, controllable and safe printer industry chain in China.
More printer-securing tips in here.
References
- Smith, Privacy and security fanatic,
https://www.csoonline.com/article/3165419/hacker-stackoverflowin-pwning-printers-forcing-rogue-botnet-warning-print-jobs.html, 05 February 2017
- Joe Tidy,PewDiePie printer hackers strike again,
https://www.bbc.com/news/technology-46552339, 16 December 2018



Leave a Comment
Want to join the discussion?Feel free to contribute!